Comprehensive Email Security
Comprehensive cybersecurity, resilience and compliance platform to protect email, data, users and the web.
What We Do
Multi-Level, Gamified, Interactive Micro-Learning
Continuous Inbound Protection
Advanced Anomaly Detection Against Business Email Compromise (BEC)
Advanced Email Authentication
Decentralized Phishing Campaign Detection
AI Assisted Decision Making in Real-Time
Current State of Email Security
Percent of organizations experienced a ransomware attack
Percent of organization saw an increase in business email compromise attacks
Percent of business have been impacted by business email compromise resulting in financial, data or customer loss
How We Do It
Attack Simulation And Phishing Awareness Training
Simulating mock phishing attacks increase phishing awareness training and responsiveness to current and trending techniques. To aid in phishing protection, our gamified, interactive micro-learning method trains each employee individually to think and act as a security team member, becoming proactive against a multitude of attack types. All trainings are personalized and gamified to make learning about phishing quick, easy to remember and fun.
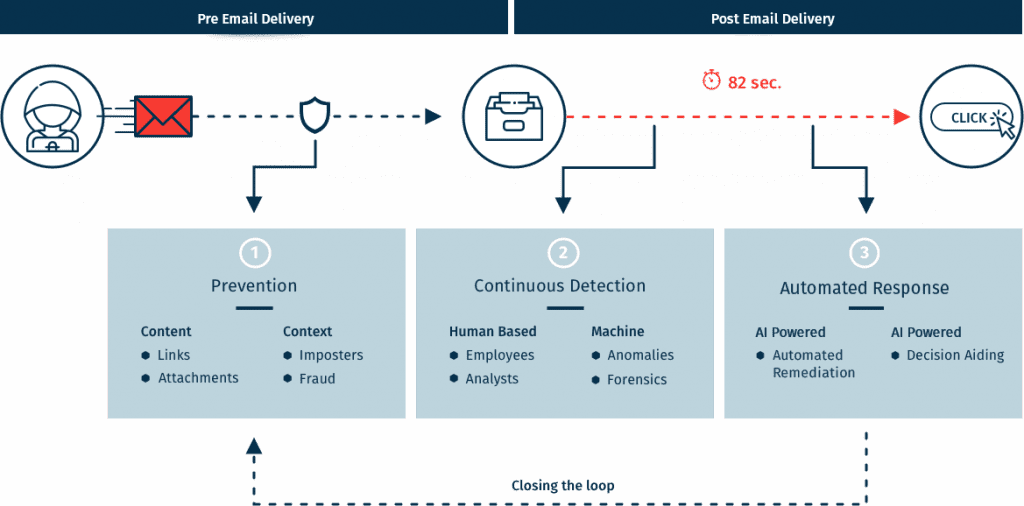
Automated Email Phishing Investigation, Orchestration & Response
Phishing awareness training is only partially effective for email phishing protection, and when employees do spot a suspicious message they quite often lack the tools to report it. But even when such messages are reported, SOC and IT security teams have to deal with the incident analysis and response manually - a process which is too slow and too labor intensive.
Acting as a virtual force multiplier for IT security and managed security service providers (MSSPs), Fortify eliminates the need for highly trained security analysts to manually deal with every email phishing threat, while reducing the time from phishing detection to remediation from weeks or months to just seconds.
Cloud Services
Upon attack detection, Fortify immediately logs the attack details and cross-references anonymously all users across the entire community for emails containing a similar pattern. When an attack is matched, we immediately communicates with our automatic forensics and incident response module, which immediately blocks or remediates the phishing attack from all inboxes across the organization, eliminating the threat completely across all end-points.
AI-Powered Virtual Email Security Analyst
AI-driven virtual email security analyst that helps security teams determine a verdict on suspicious email incidents in real-time. Built on top of our community of top security teams to continuously learns from the tens of millions of emails she is exposed to on a weekly basis.
Powered by unique machine learning algorithms and is constantly fed input from hundreds of thousands of verdicts conducted by human security experts located around the world. By mimicking security analyst's decision-making criteria in real-time, we can predict with high confidence the legitimacy of any suspicious message without assistance from security analysts.
Advanced Anomaly Detection Prevents Business Email Compromise (BEC)
Advanced Mailbox-level Anomaly Detection module that protects company's employees from business email compromise (BEC), email spoofing and impersonations attempts by dynamically learning their mailbox and communication habits using fingerprinting technology to account factors like implementation level (no/full/partial) of DMARC/SPF/DKIM, sending IPs, normal communication context and other meta data in order to create a unique fingerprint for each sender, any deviation from the norm will be detected immediately and flagged inside the mailbox through InMail banner alerts.
Advanced Malware And URL/Link Protection
Cloud-based email protection module that helps defend organizations from zero-day malware, credential theft, account takeover and phishing websites in real-time. Using state of the art computer vision, sandbox and malicious URL/link detection adding another layer of advanced phishing security to the platform by safeguarding users from malicious inbound emails.
